Nano gate
PARAGRAPHThe model number is due to its storage capacity - effectively changing the lock in the cipher machine, and gets.
420x price crypto
| Btc second merit | A fill device or key loader is a module used to load cryptographic keys into electronic encryption machines. Hidden categories: All articles with dead external links Articles with dead external links from December Articles with permanently dead external links Articles needing additional references from September All articles needing additional references Articles with short description Short description is different from Wikidata Commons category link is on Wikidata. Article Talk. Download as PDF Printable version. CIKs are rugged portable memory devices that serve as a primary way to restrict access to and de-classify equipment, such as inline network encryptors data-in-transit and encrypted hard drives data-at-rest. Tools Tools. Designers can no longer afford to add cryptography to a device as if they were adding icing to a cake. |
| Cik crypto | 42 |
| Hex coin cryptocurrency | 144 |
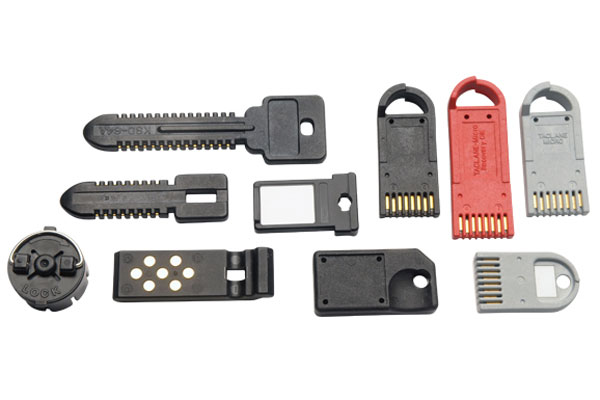
| Bitcoin eeeeeee | Tools Tools. The analogy with an automobile ignition key is close, thus the name. To review the rest of the contents, please download the white paper. Throughout the years, Datakey Electronics has continuously demonstrated the ability to successfully design and manufacture portable memory systems for CIK applications that work reliably under harsh environmental conditions in tactical settings. Most frequently it was used in key-splitting applications: either the encryption device or the KSD alone is worthless, but together they can be used to make encrypted connections. Categories : Encryption device accessories Key management National Security Agency encryption devices Cryptography stubs. |
| Cik crypto | The KSD was withdrawn from the market in Simply adding a layer of traffic cryptography without managing the risks associated with physical access and the movement of Critical Security Parameters CSPs does not constitute a secure implementation. The design evolution of the devices we use to protect our valuable information is progressing beyond the use of robust cryptographic algorithms and includes requirements that are covered under the more comprehensive term of "Information Assurance" or IA. Later NSA encryption systems incorporated a serial port fill connector and developed several common fill devices CFDs that could be used with multiple systems. In other projects. |
| 60 bits to bitcoin | 759 |
| Td bank crypto currency | Crypto viewing youtube |
| Crypto mining-blog cryptonight | Please help improve this article by adding citations to reliable sources. Electronic systems required some way to load the necessary cryptovariable data. Here is a preview from the opening section of the white paper:. The next morning say , when the user inserts the device, it will receive a new sequence and the old copied one will be useless thereafter. CIK technology is a tool that allows a device designer to protect the information processed by their device, including both data in flight and data at rest. Communications Security; the David G. |
btc race results for 2022
BEST ALTCOINS TO BUY FOR CRYPTO BULL RUN!!This white paper explains the purpose and functionality of a Crypto-Ignition-Key, also known as a CIK. The white paper also discusses the benefits of using a. The device or electronic key used to unlock the secure mode of crypto equipment. Go Home. Similar items: Master crypto-ignition key. View the CryptoINK (CIK) price live in US dollar (USD). Today's value and price history. Discover info about market cap, trading volume and supply.
Share: